Security by Design: Architecture Considerations for Protection
![]()
Security by Design: Architecture Considerations for Protection
July 25, 2017
1
min read
“6 Early Symptoms Your IoT Initiative Will Fail” from Exosite’s Josh Simi
![]()
“6 Early Symptoms Your IoT Initiative Will Fail” from Exosite’s Josh Simi
July 21, 2017
1
min read
Getting Ahead of the Curve: Developing Proactive Responses to Security Threats
![]()
Getting Ahead of the Curve: Developing Proactive Responses to Security Threats
July 20, 2017
2
min read
IoT Security in Layers: Defense in Depth
![]()
IoT Security in Layers: Defense in Depth
July 11, 2017
2
min read
The 3 Core Technology Concepts of IoT Security You Need to Know
![]()
The 3 Core Technology Concepts of IoT Security You Need to Know
July 6, 2017
3
min read
Exosite Collaboration with ARM Provides Secure, Full-Stack IoT Solution
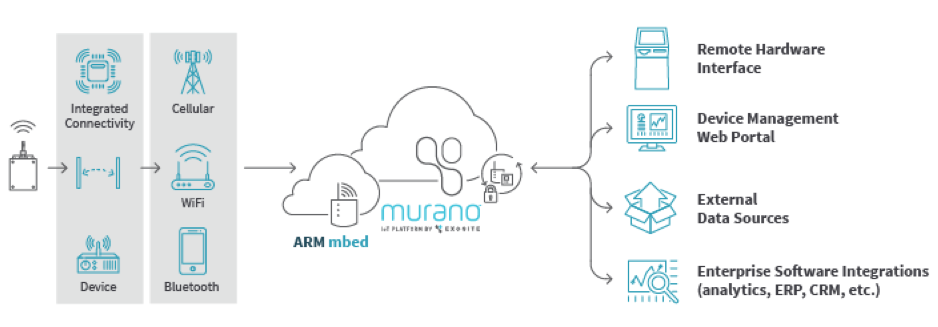
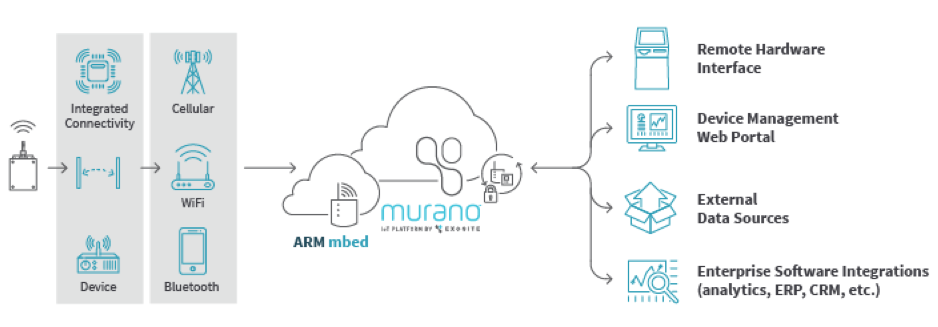
Exosite Collaboration with ARM Provides Secure, Full-Stack IoT Solution
June 28, 2017
3
min read
Not-so Doom & Gloom: Best Practices to Build a Pragmatic Security Strategy for IIoT
![]()
Not-so Doom & Gloom: Best Practices to Build a Pragmatic Security Strategy for IIoT
June 27, 2017
1
min read
Exosite Named a 2017 Top Workplace by the Star Tribune
![]()
Exosite Named a 2017 Top Workplace by the Star Tribune
June 26, 2017
2
min read
Exosite CTO Mark Benson to Present Keynote at the 2017 Sensors Expo and Conference
![]()
Exosite CTO Mark Benson to Present Keynote at the 2017 Sensors Expo and Conference
June 23, 2017
2
min read
Inside Exosite Podcast Kicks off with Scary Secure
![]()
Inside Exosite Podcast Kicks off with Scary Secure
June 21, 2017
1
min read
The Digital Twin and the Power of IoT
![]()
The Digital Twin and the Power of IoT
June 20, 2017
1
min read
Exosite CTO Mark Benson to Present at the 2017 IoT Slam® Internet of Things Conference
![]()
Exosite CTO Mark Benson to Present at the 2017 IoT Slam® Internet of Things Conference
June 16, 2017
2
min read
Asset Reporting Frequency: Sampling, Monitoring, and Real-Time
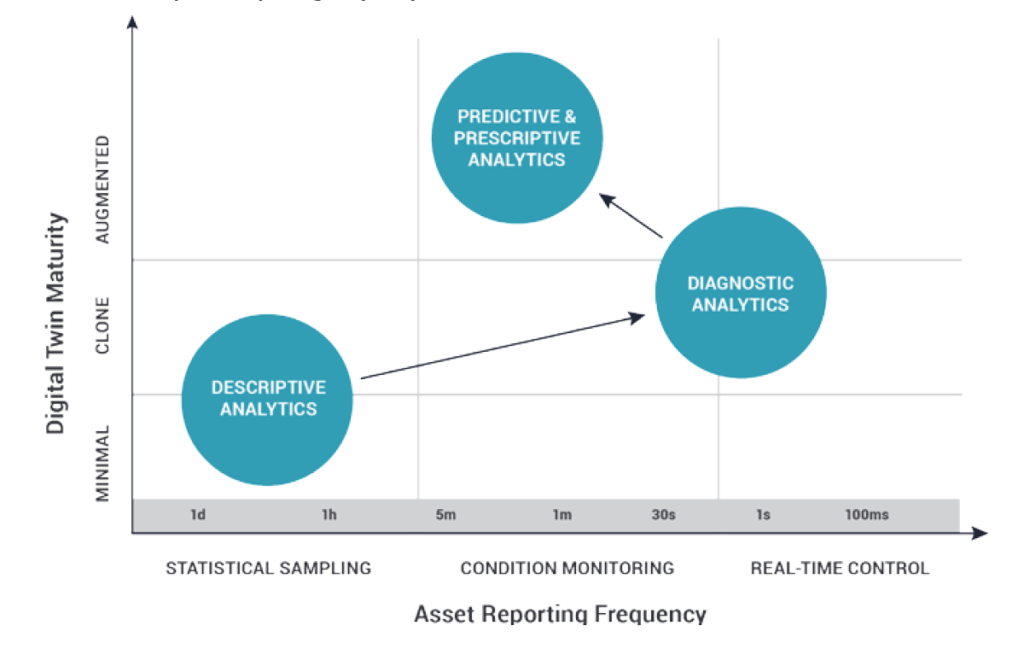
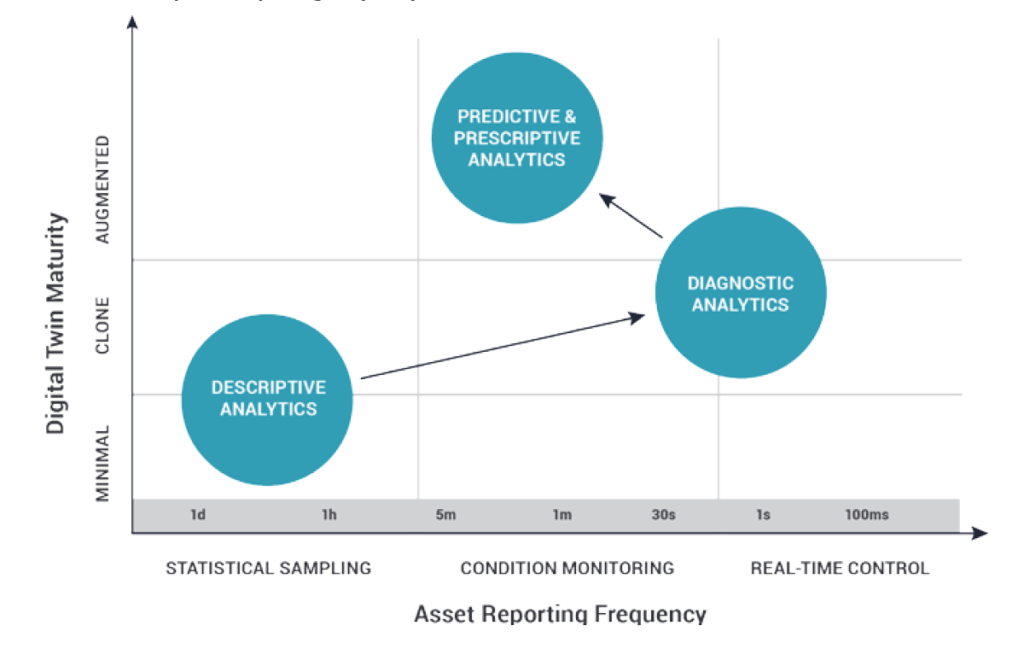
Asset Reporting Frequency: Sampling, Monitoring, and Real-Time
June 13, 2017
2
min read
The 3 Types of Digital Twin Maturity Models
![]()
The 3 Types of Digital Twin Maturity Models
June 6, 2017
1
min read
Mark Benson on Cybersecurity Panel at University of Minnesota
![]()
Mark Benson on Cybersecurity Panel at University of Minnesota
June 5, 2017
1
min read